Cybersecurity Sentinel Whitehat Hackers
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money from users; or interrupting normal business processes.
Implementing effective cybersecurity measures is particularly challenging today because there are more devices than people, and attackers are becoming more innovative.
Cybersecurity is important because it protects all categories of data from theft and damage. This includes sensitive data, personally identifiable information (PII), protected health information (PHI), personal information, intellectual property, data, and governmental and industry information systems.
Without a cybersecurity program, your organization cannot defend itself against data breach campaigns, making it an irresistible target for cybercriminals.
The field of cybersecurity is growing rapidly due to the increasing number of cyberattacks and the need for organizations to protect their digital assets. Cybersecurity professionals work to safeguard an organization's computer systems and networks by implementing security measures such as firewalls, encryption, and intrusion detection systems. They also monitor for potential threats and respond to security incidents when they occur.
There are several different types of cybersecurity, including network security, application security, information security, operational security, and disaster recovery/business continuity planning. Each type focuses on different aspects of protecting an organization's digital assets.
Overall, cybersecurity is a critical component of modern business operations and is essential for protecting sensitive information and maintaining the trust of customers and stakeholders.

The Cryptographic Horror Show
Welcome to the brave new world of the Baud and Byte, the Trap and the Delight.
Fright Night 101
Keyloggers snitch, while exploit-zero botnets swarm and pitch. Without a click, the sermon knocks on the door, a Gruesome Gollum Goblet arrives with a USB drive, stating 'PLUG ME IN, I'M PRECIOUS.'
Your patches resemble broken fragments upon a busted mirror, jagged sharp fragile ego messes they are, where decayed band-aids attempt to patch a sinking ship, and hatches are breached by titanic trolls, who are laughing at the mess they helped create.
The Digital Jungle Exists: What is Free and What is Private?
What is Malware?
Malware: Communication weaponized to wreak havoc—data turned dagger.
What is Communication?
Communication: Ones and zeros flowing, the lifeblood of our cyber veins.
What are Ones and Zeros?
Ones and zeros, bits and bytes: The building blocks, stacking into secrets or sabotage.
What is Data?
Data: Raw info, the currency of this digital landscape, the concrete urban, chaotic jungle.
Regardless if an IoT device is hardware with a plug, a wireless or Bluetooth device, they all contain information.
What are IoT Devices?
IoT devices: Plugged, wireless, Bluetooth—each a potential Pandora’s box, spilling info if it can transmit.
But, here's the thing, do you not realize there are other modes of transfer besides WiFi, Bluetooth, and the plug? That is what you see, but tell that to the Titanic, and she will testify from the depths of despair of the murky bottomless sea. It is not what you see, but that which you do not see, that which you do not know!

Did you understand what I am suggesting? It contains a cryptographic riddle: any device we have can contain malware, and it doesn't even need to be plugged in. For instance, if the device is Bluetooth compatible and requires device drivers to be installed or downloaded from the internet, what else is being transmitted?
A binary Bluetooth breeze carries a whisper, full of screaming ones and zeros, a data stream that should be harmless—until it morphs into the monstrous blizzard malware maelstrom of a storm.
Devices buzz, they shake, they rattle, roll, and hum, unplugged yet very much alive, sitting waiting, listening for any signal to be detected.
That broadcasted message cries for attention, a signal abnormality, hijacked by titanic trolls cackling from the shadows, lurking behind someone else's technological set of skills.
The air crackles with an abhorrent encrypted threat, a sinking ship is the bitcoin, cryptographic bet.
To cast a lot of IoT gadgets, sent out from the cradle, transmitted data well beyond the grave, the rootkit patch has been contaminated by corrupt hands, an ancient old evil, band-aids offer no protection.
To dance upon the stars, drinking from silver goblets, cups toasted high in admiration of their insecure egos, even Dorian Gray takes notes, mirrors come crashing down, shattering under their strain.
The riddle spins: if it can transmit information, it can transmit information. The question is: what information is being transmitted, and to whom shall receive it openly or unwillingly?
If it can transmit data, it surely can transmit malware—a chilling frozen truth, trapped deep beneath the Siberian Tundra.
The Binary Trap House, a sweatshop full of baud and byte slave labor workers.
A wireless speaker, a smartwatch, a driver download—all conduits for a hidden "PLUG ME IN, I’M PRECIOUS" USB interceptor, knocking on your digital door.
Mad Max with a high-rise manifold and blower cannot keep up with the current advancements of the increase and explosion of knowledge, information, and technology.
The frostbite deepens, cooling the havoc with a cryptographic chill, yet the heat of the unknown lingers.
Shall hell freeze over first, before the stock market comes crashing down?
Malware: Communication weaponized to wreak havoc—data turned dagger.
Communication: Ones and zeros flowing, the lifeblood of our cyber veins.
Ones and Zeros: The building blocks, stacking into secrets or sabotage.
Data: Raw info, the currency of this jungle.
IoT Devices: Plugged, wireless, Bluetooth—each a potential Pandora’s box, spilling info if it can transmit.
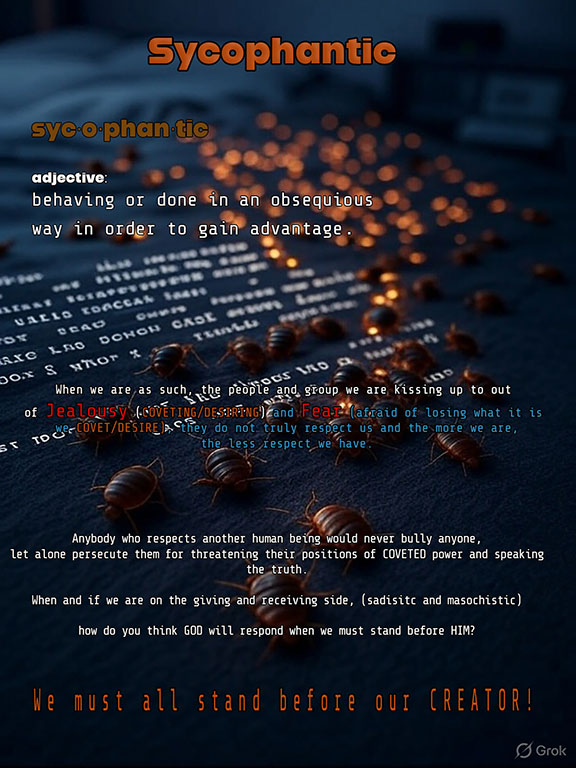
Malware’s the internet bedbug infestation, and rootkits are the gift that keeps on giving; like the cursed fruitcake nobody asked for.
The viral freeze, chillin' like a villain on penicillin, please.
Parasitic arsenal weapons dressed up as friendly web tokens, releasing more havoc than a bed bug has friends.